Best Practices für heylogin Organisations-Admins

heylogin makes it much easier to handle passwords, whether for private or business purposes. However, when working in a company, you should pay attention to a few things as an organization admin so that you always remain in control. This article gives you an overview of the most important things you can do as an admin. Let's start with the most important point: recovery.
Two admins for recovery
You should at least 2 organization admins have in your organization. This ensures that access to the organization is still guaranteed even if an admin loses access, for example due to a defective smartphone.
If you are the only admin and lose access, heyLogin Support can usually no longer help. Since the heylogin organization is linked to the admin account, the entire company can lose access in the long term.
If you want to further protect yourself or do not have the capacity for multiple administrators, there are other methods to further secure account access. In addition to the backup functions of heylogin and smartphone, additional devices can also be set up to unlock.
Yubikey as an emergency key
In addition to the smartphone, heylogin also offers other options for unlocking your web session. In addition to device-specific technologies such as Windows Hello and Apple's Touch ID, this also includes the Yubikey.
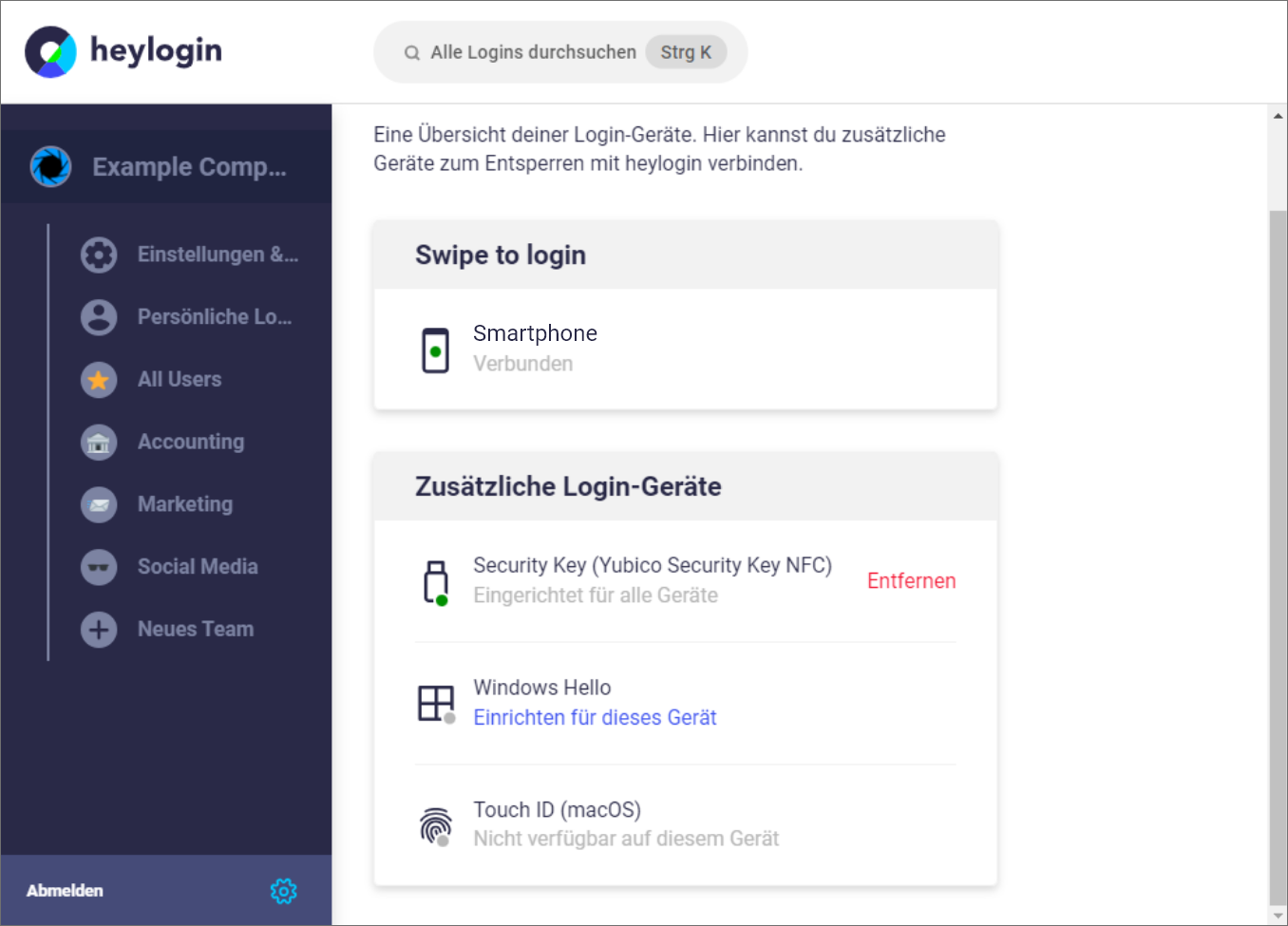
All alternatives allow access to the account through an alternative 2 factor, but with Windows Hello and Touch ID, this only works on devices that also support this feature.
Although the Yubikey must be purchased separately, it allows the account to be unlocked across devices and is therefore particularly useful in an emergency.
Restrict accesses
Regardless of whether you use an ISMS (information security management system) in your company or not, it always makes sense to restrict employee access to relevant logins. This is possible, for example, via access rights in heylogin:

In addition, it is important to regularly check whether all employees only have access to the logins that they really need. This means that regularly checking the teams and seeing whether every member should still have access to them is an important work routine.
heyLogin guidelines for employees
In the work environment, errors can occur when using new software, no matter how easy it is to use. In order to optimally prepare your users for using heylogin, you can simply share the information in the following section and, if necessary, adapt it to your company situation.
Personal logins and teams
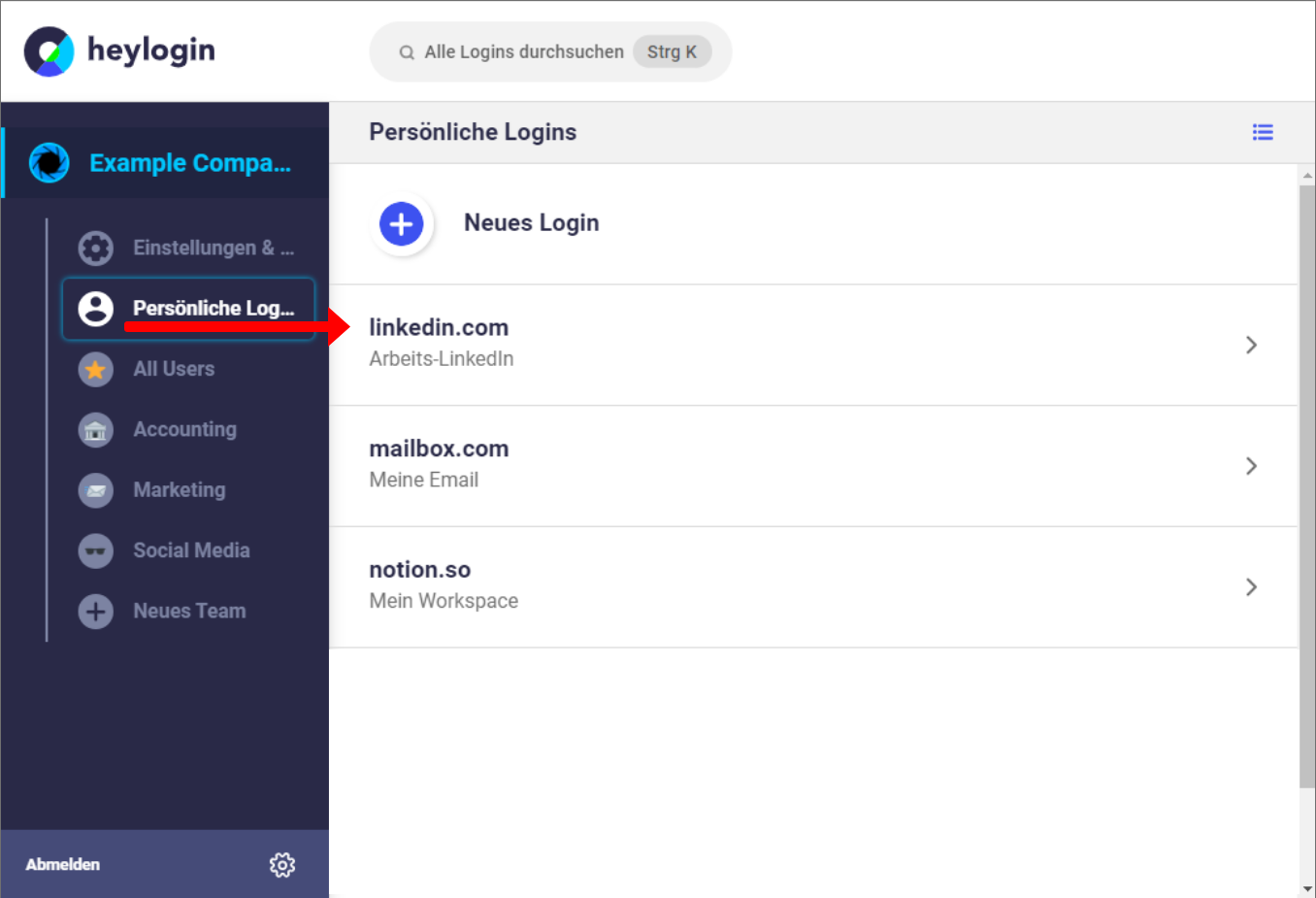
Personal logins are:
- only for individual users
- reserved for individual logins (own work email, etc.)
- are NOT intended for private logins
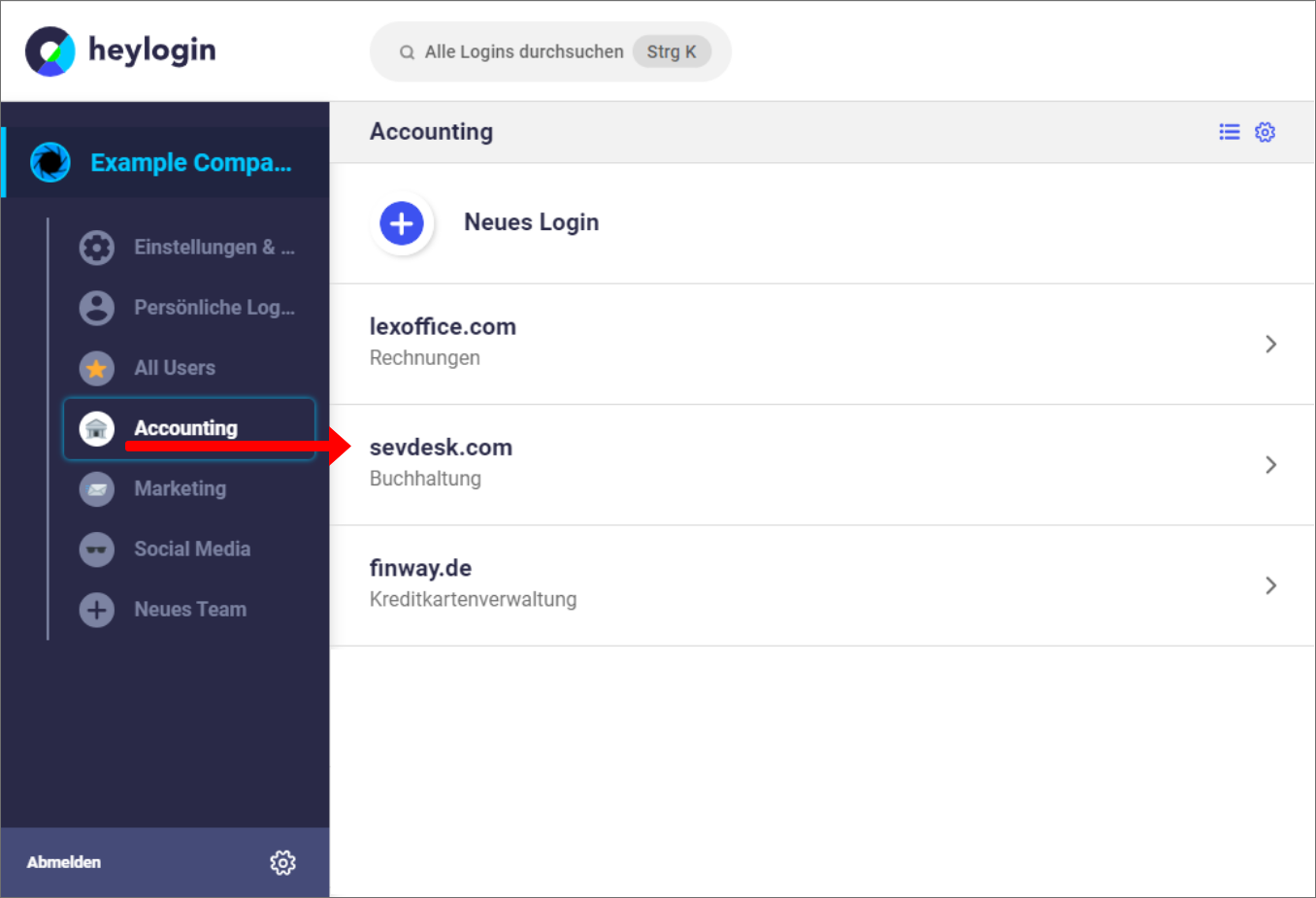
Teams are:
- Areas where logins can be shared
- best sorted by subject area (marketing, accounting, etc.)
- collection points for sensitive data, so only people who actually need it should have access
Share logins
Logins are shared via the team function. Only users who really need access should be invited to join the team. Access rights can further restrict the visibility of the password and sharing.
This feature is not intended for sharing private logins.
Private use
heylogin can also be used for private use. To do this, you can create a private account in the settings. The private account is separated from the organizational account.
However, this also means that if a smartphone is lost, the admin cannot disconnect the device and reconnect the user. When creating a private account, you therefore have to take care of various backup functions yourself. Using our backup code, for example.
Important: a private account is not created automatically. As an admin, you can invite new members to the organization via email, so there is no need to create a private account by the new user.
Bonus: Set login location
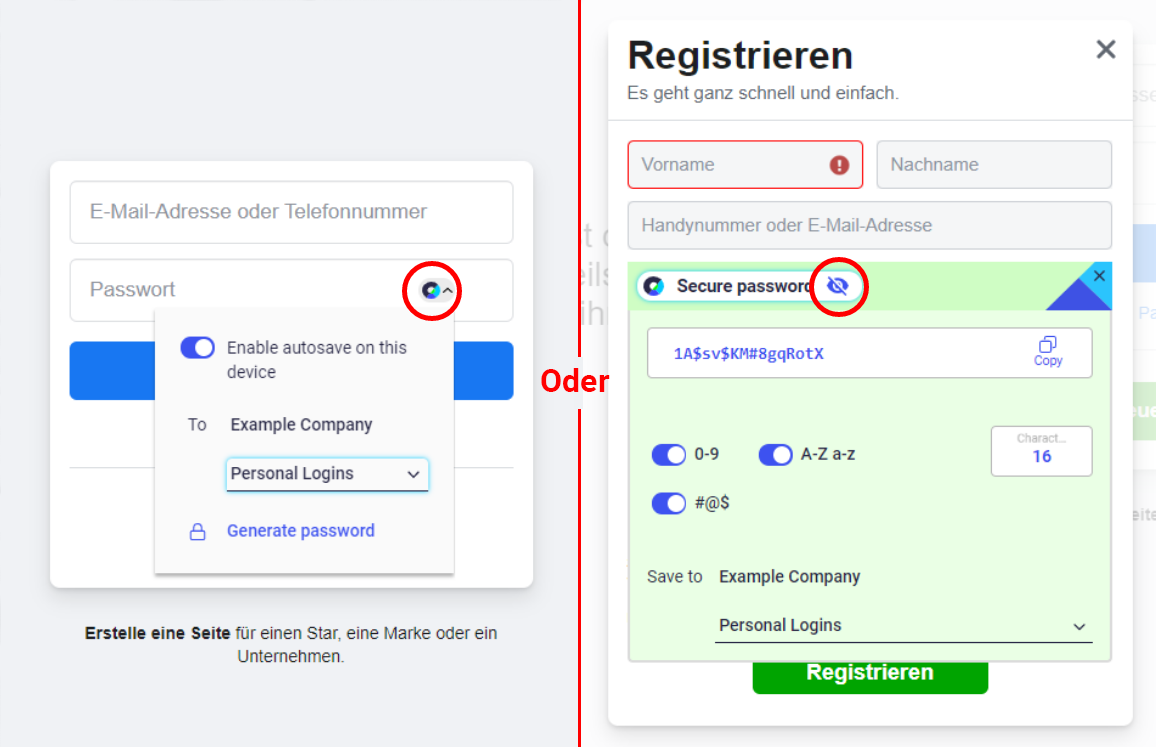
When generating a new login directly on a website, a storage location can be defined. Either just for this one time, or as a standard for every login generated. This works both when signing up for websites using the heylogin icon or when generating passwords via an overlay (you have to click on the eye icon to do this). All users must set this for their own account.
These were our best practices for organizational admins. If you have any further questions, requests or problems, please either contact your heylogin representative or write to our support team.

.svg)